Businesses and individuals often see email as the go-to communication channel (unless you’re texting your grandma, that is). Unfortunately, by default, email is not the most secure.
To remove this risk, nowadays we use email encryption. But what exactly is this process and how does it work? Keep reading to find out!
What is email encryption?
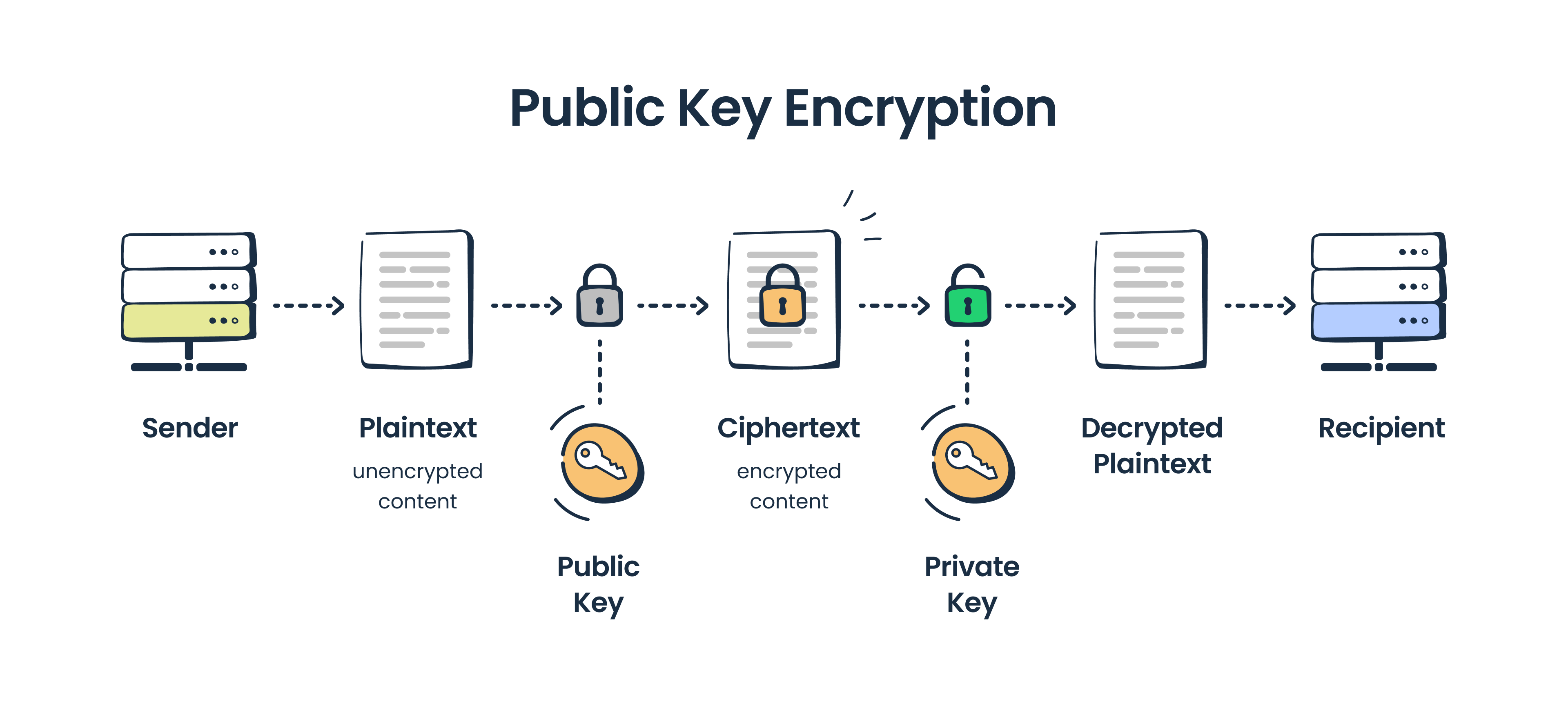
Email encryption, simply put, is a process that turns email content into scrambled ciphertext. But if we were to be a bit more formal, we can describe email encryption as converting email plain text into a coded format that requires a correct key to be decoded.
Many email providers have been implementing email encryption for years to safely transmit email messages between a sender’s and recipient’s email server. But why all this hassle?
Well, you see, when an email is encrypted, the sensitive information within it cannot be read by third parties without permission. So, if a malicious actor were to intercept an encrypted email and try to look at not only its information but also its attachments, they would find only unreadable text. This process of scrambling data to shield it from interceptors is very similar to what is VPN used for on a broader network level.
Not so useful for the malicious actor now, is it?
What is an encrypted email?
We all know what an email is – a digital message sent electronically via the Internet containing text, attachments, and other multimedia elements. An encrypted email, on the other hand, can be defined as a digital message that has been transformed into an unreadable format in an effort to protect its contents.
What is the difference between an encrypted and an unencrypted email?
The key difference between an encrypted and an unencrypted email lies in the level of security and privacy each provides.
An encrypted email is designed to protect its content from being accessed by unauthorized individuals. This involves encoding the content so it can only be decoded with a proper key, often as part of a broader security strategy that may also include practices like container image scanning to identify vulnerabilities across digital assets.
In contrast, an unencrypted email remains in plain text format, making it easily readable by anyone. Startups increasingly work with providers offering cybersecurity services for startups to implement layered email security that combines encryption with phishing protection and authentication protocols. This lack of protection means that sensitive data contained in unencrypted emails is vulnerable to eavesdropping, attacks by hackers and cybercriminals, as well as data breaches, thus posing significant risks to privacy and enterprise cybersecurity.
How email encryption works
There are two common types of email encryption:
- Encryption in transit (you probably know it as TLS/SSL/STARTTLS)
- End-to-end email encryption or public key encryption
TLS encryption
TLS stands for Transport Layer Security and it, as its name suggests, protects emails during transportation. Securing these server-to-server connections is a core concern of machine identity management, which ensures that the certificates and keys used by email servers to authenticate one another remain trusted and valid. It is a reliable method used by default in many email clients, such as Gmail and Yahoo. TLS is also known as basic encryption, as it secures the message transition channel, not the message itself.
How does TLS work, and how do you enable it?
To establish a TLS secure connection, the STARTTLS command is used. This command instructs an email server to switch to a secure connection via TLS or SSL (SSL, or Secure Sockets Layer, is a TLS predecessor) and is compatible with SMTP and IMAP protocols.
To be able to use STARTTLS on your email client or server, you usually need to set the proper configuration in the server settings. Another thing to keep in mind is the dependency on ports — port 465 is mainly used for Implicit SSL/TLS, while port 587 is more common for Explicit SSL/TLS. What’s the difference?
- With Implicit or Forced SSL/TLS, a sender’s server sends a request to a recipient’s server for establishing a secure connection. If the recipient’s server doesn’t support TLS and the exchange of the encryption keys can’t be performed, data transition won’t be allowed. This means that the email won’t be sent at all.
- With Explicit or Opportunistic SSL/TLS, a sender’s server also sends a request to a recipient’s server for establishing a secure connection. However, in this case, if the recipient’s server is not compatible and the secure connection can’t be established, data transition will happen anyway, but via an unencrypted channel.
For more details on email encryption in transit, read our STARTTLS vs SSL vs TLS blog post.
End-to-end encryption
End-to-end encryption utilizes a pair of digital keys — a public and a private one. Your public key is connected to your email address and is accessible to other people so that they can find you and send you encrypted emails. To decrypt the emails, you, as the recipient, need to use your private key, which is stored safely and is available only to you.
There are a few types of solutions and protocols that ensure end-to-end email encryption:
S/MIME
S/MIME stands for Secure/Multipurpose Internet Mail Extensions and provides so-called asymmetric encryption implemented with S/MIME certificates. S/MIME allows you to encrypt and digitally sign emails so that only intended recipients can decrypt them and access their content.
When it comes to keys, S/MIME uses a set of public and private keys that have to match:
- The public key is used for authentication and is sent with each message to identify the sender.
- The private key is used for decryption but also for generating a digital signature.
To send someone a S/MIME encrypted email you have to receive their digital signature first. Also, you need to obtain S/MIME certificates from the certified authorities — S/MIME is mostly used inside organizations, so business email providers usually have this encryption option included. Along with that, there are third-party authorities that offer S/MIME certificates.
Gmail and Outlook come with S/MIME encryption available in their business subscription plans, while for iOS users, it’s universally available.
OpenPGP
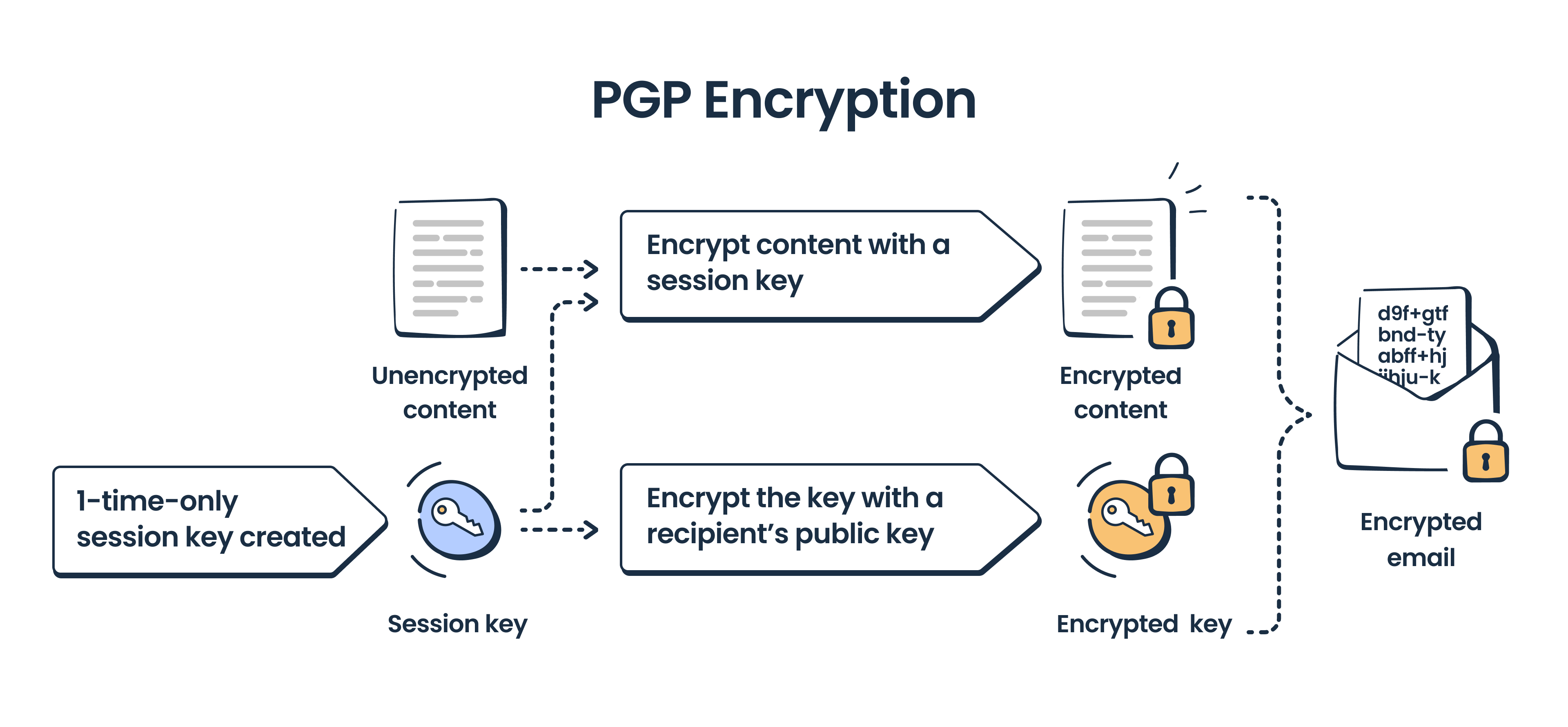
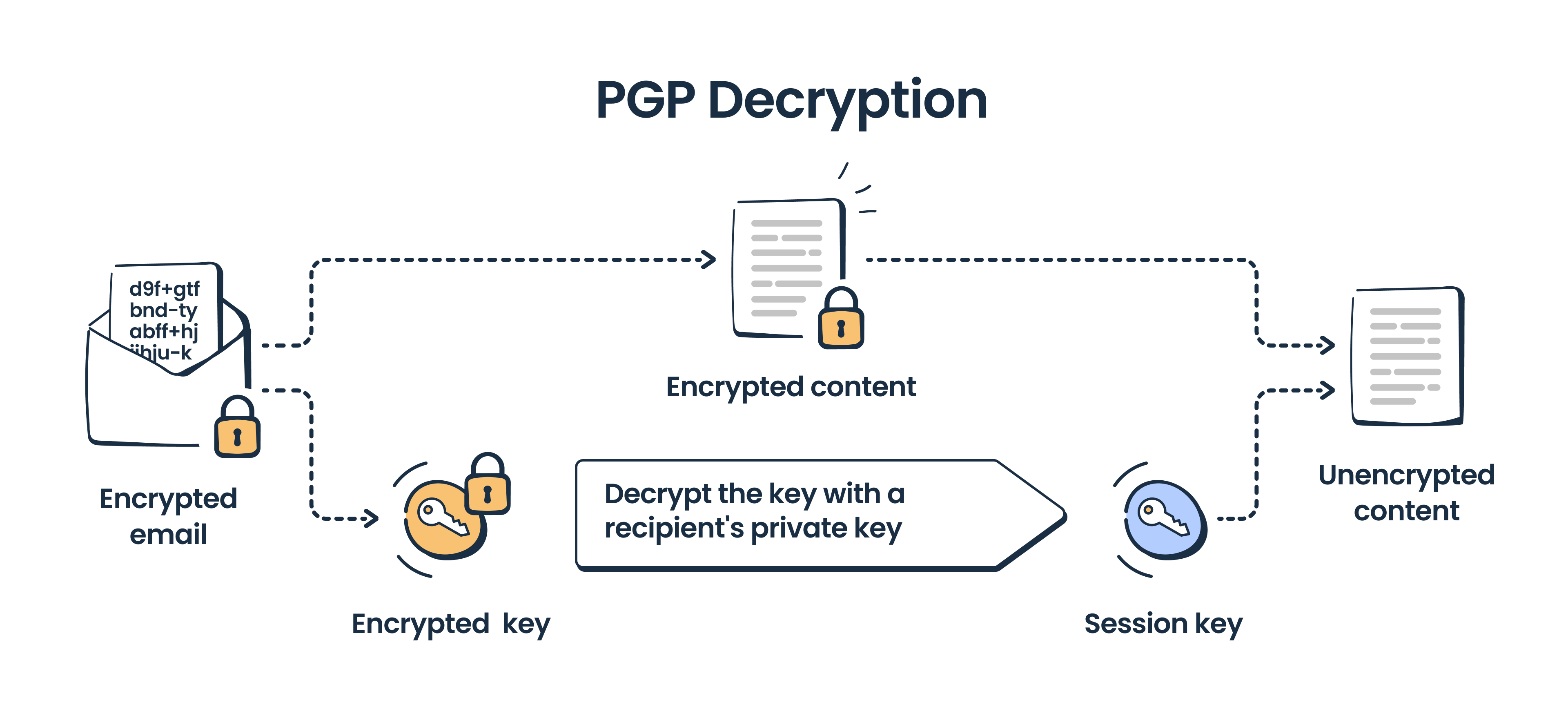
OpenPGP is a widely used encryption standard (particularly in personal email communication) created to secure not only emails but also texts, files, and entire directories. It was introduced in 1991 alongside the Pretty Good Privacy (PGP), which was the first public-key cryptographic program to become widely accessible.
OpenPGP encryption features digital signatures and relies on a set of private and public keys, similar to S/MIME. But, unlike S/MIME, PGP uses a combination of symmetric and asymmetric encryption. Symmetric encryption, where the same key is used to both encrypt and decrypt a message, is employed for the actual data. However, this symmetric key (session key) is then encrypted with the recipient’s public key using asymmetric encryption.
Symmetric encryption is significantly faster than asymmetric encryption, but it needs an additional layer of key encryption for enhanced security.
Bitmessage
Bitmessage is a peer-to-peer communication protocol for sending encrypted messages designed on the principles of Bitcoin. The protocol is also decentralized which means means that Bitmessage doesn’t utilize and doesn’t depend on central servers or certificate authorities.
For encryption, Bitmessage uses a set of corresponding public and private keys. It encrypts emails with the recipient’s public key, but it doesn’t expose any information about the message sender or its recipients. Therefore, as there is an anonymized recipient, every message is delivered to each member of the Bitmessage network, but only the intended recipients are able to decrypt it with the matching private key.
To use Bitmessage, you need to install a Bitmessage client. For other information, refer to the project’s page on GitHub.
How to send encrypted emails
In general, there are three main approaches to sending encrypted emails:
- Programmatic (we touched upon this in the OpenPGP section)
- Switching to an encrypted email provider
- Sending with your regular email client but using a built-in email encryption solution or a third-party plugin/email encryption service
Encrypted email providers
Encrypted email providers offer specialized services that protect your email communication through robust encryption techniques. This usually involves using the public key infrastructure (PKI), where the sender encrypts the email with the recipient’s public key, and the recipient decrypts it with their private key.
When it comes to your choice of encrypted email providers, we have an article dedicated just to that, so make sure you check it out.
For this article, we’ll list a few popular options:
- An email client available as a web and mobile app. It features end-to-end encryption, a user-friendly interface, and a generous free plan to start with.
- Similar to ProtonMail, this email client focuses on security and privacy. It provides end-to-end encryption and is available on both web and mobile platforms.
- Another secure email client with encryption features. It supports web and mobile access and is known for its simplicity and ease of use.
If your business requires compliance with particular standards, such as HIPAA, for the medical industry, you should search for a dedicated solution such as a HIPAA-compliant email provider. In this category, you will find specialized healthcare software, such as Paubox, and other business solutions, such as Virtru, certified for use in healthcare communications.
On the server side, companies like Guardian Digital provide email encryption using TLS as well as cloud email security protection from advanced threats, including ransomware and phishing attacks.
Common email clients
By default, the majority of email clients ensure TLS encryption. But, if you need end-to-end encryption, then you’ll need to make additional configurations.
For instance, Outlook, Gmail, and Apple Mail support S/MIME (with restrictions), while Yahoo doesn’t have any end-to-end encryption forcing its users to go for a professional plugin to enable it.
Now, let’s look at encryption within the top three email clients:
Email encryption in Gmail
In your Gmail email account, you have the option to encrypt your messages with the S/MIME standard; however, this is available only for Enterprise, Education Fundamentals, and Plus edition users. So, if you are using any one of these, you can configure S/MIME in the admin console and then upload certificates obtained from a trusted authority (see the full list in the Google documentation). Note that both the sender and recipient must enable S/MIME and exchange certificates to be able to exchange encrypted messages this way.
If you are using Gmail on a personal plan but still need to send encrypted messages or prefer other encryption standards, we recommend picking a third-party plugin, such as Virtru or FlowCrypt.
Also, avoid using Gmail confidential mode. This mode, while it protects your messages from forwarding, copying, downloading, etc., is not secure, and when using it messages still get stored on Google servers.
Email encryption in Outlook
There are three main options when it comes to Outlook encryption: S/MIME, Microsoft 365 Message Encryption (OME), and third-party services.
S/MIME encryption is available for all Outlook users that have Outlook 2010 or a later version (this excludes Outlook on the web on Mac, iOS, Android, or other non-Windows devices).
To enable S/MIME in Outlook, you need to configure certificates first. These can be obtained from the Windows-based Certification Authority or a third-party authority.
Microsoft 365 Message Encryption (OME) is available for Microsoft 365 Enterprise E3 users and combines email encryption and rights management capabilities by Azure Information Protection.
Email encryption on macOS and iOS devices
Apple Mail, the default email app on macOS and iOS devices, features built-in S/MIME encryption. To use it, you don’t need to load any additional certificates. Instead, you just enable Encryption in the advanced settings, and if both you and your recipient belong to the same Exchange environment, you can start messaging right away. If you are not inside the same Exchange environment, then you need to install encryption certificates for this recipient. These are available inside the Apple Mail functionality.
Alternatively, you can always use extensions for OpenPGP encryption or switch to a secure email client, such as Canary Mail.
Final words
Sending emails is often much more complex than we think, and email encryption is at the very heart of the process.
TLS encryption is what protects the majority of our emails, while for corporate communications or sending sensitive personal information, end-to-end encryption and the extra effort it requires is a must.
Luckily, as data protection is of high importance these days, you have a wide range of options for sending and receiving encrypted emails. We hope that after reading this article, you can easily decode which method and tool that best suits your needs!
For more email security content gems, keep following our blog as well as our YouTube channel featuring insightful content such as the video below: